The beginning of February this year brought along bad news for warm-weather fans: beloved groundhog, Punxsutawney Phil, saw his shadow.
The famously prophetic creature returned to his den shortly after emerging early that February morning. With his behavior, the groundhog indicated that winter would stick around for another six weeks. Unfortunately for the sun lovers, winter did stick around this year.
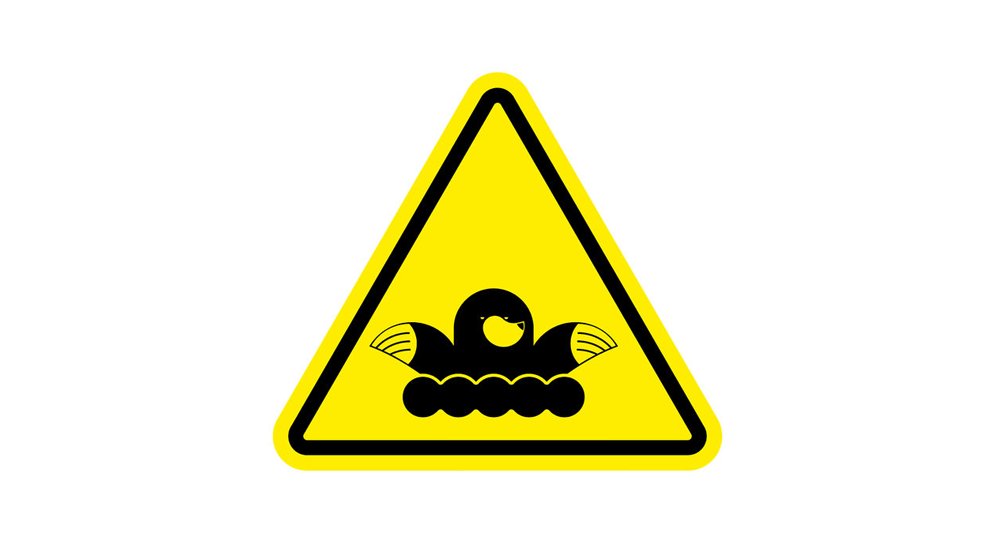
Meanwhile, a few hundred miles away in New England, an entirely different animal took on a different prediction task in the form of a mole. Not just any mole, one of our own, CloudShare account executive, Mitch Goldstein.

The participants were trained on how to handle advanced cyber warfare activities and were required to complete an end-to-end incident response plan. The NECYR training included skills like network forensics, incident training, vulnerability research and reverse engineering, open source data collection, intelligence production, and more.
Here is where Mitch was tasked with his new role (the mole). You see, the cyber range experts needed a mole for their training scenario. They secretly chose Mitch to be the insider threat – playing the part of an ill-intent systems engineer who had become vengeful after an argument over pay and responsibility. They transformed CloudShare’s honorable Mitch into a villain and had him maliciously inject the system with a real-time attack.
Mitch had joined the class to see how participants train on complex network environments and experience CloudShare’s virtual labs in action. He was super-impressed with the detailed scenarios, the expertise of the trainers, and the real-world environments. While perhaps not a true mole, Mitch learned a great deal and enjoyed seeing the students unveil and resolve the crisis he created.
It is no secret that complex cyber range training has turned to be mandatory for organizations. No matter how much they spend on state-of-the-art solutions, corporations can never rely on technology alone to be fully protected from cyber attacks. They need well-trained employees.
In fact, a recent article in the Harvard Business Review, entitled “The Best Cybersecurity Investment Business Leaders Can Make Is Better Training,” makes this point. With so many entry points for attack and limited skilled resources, many different teams now share the responsibility for securing data and supporting operations. And as networks continuously expand and evolve, so do the experts that must be trained to secure them. Thus, the challenge is to focus on providing the right training approach to the right people.
According to HBR’s Dante Disparte and Chris Furlow, “Cyber risk evolves according to Moore’s Law. That’s a major reason that technology solutions alone can never keep pace with dynamic cyber threats.”
In fact, according to e-Learning Industry, “in 2013, the cost of cybercrime was estimated to be $100 billion. By 2015, that number had quadrupled to $400 billion.” And Kirstjen Nielsen, Secretary of the U.S. Department of Homeland Security speaking at RSA 2018, stated, “By 2021, cybercrime damage is estimated to hit $6 trillion annually. To put that in perspective, that’s almost 10 percent of the world economy.”
Cyber attacks have now reached epidemic proportions. And the situation will continue to get worse. Nielsen makes it very clear: “the threat picture is getting dimmer, not brighter,” and “digital threats are multiplying faster than we can keep up.”
Everyone—from the largest companies to the smallest—are vulnerable.
To be prepared, organizations must improve the skills of existing employees by providing real-world training on cyber ranges – else they might find themselves having to deal with a mole – or worse, an army of them. But this time it won’t be Mitch.
Deliver Real-World Training and Grow Your Business with the #1 Virtual Training Labs Solution